Today’s sophisticated security threats require responses that are no less sophisticated and that encompass every aspect of how a system operates.
Read More
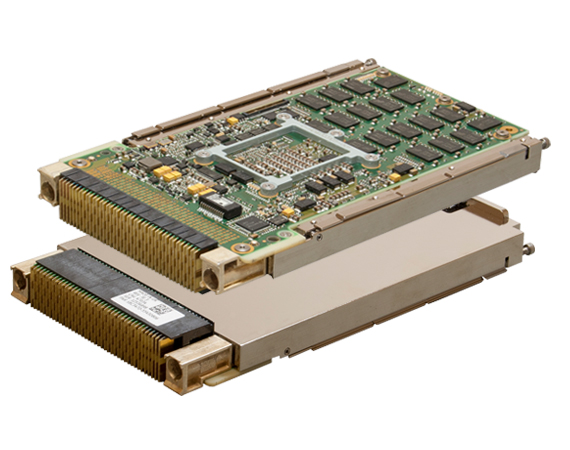
Aerospace and military systems are increasingly dependent on complex computing, communication and data storage platforms to accomplish their missions. These software-intensive systems rely on algorithms, rules, and data that, if comprised, can spell disaster for the mission and the personnel that depend on them. Ensuring the integrity of these platforms requires hardware, software and physical solutions. Abaco Systems understands the complexity of securing the hardware, operating system, applications, and data, whether it is in storage or transmission.
Secure computing is a labyrinth of technologies that ensures the intended platform performance, starting with the boot process through operating system loading to applications running. In order to provide full coverage, we offer a portfolio of products that enables system integrators to implement multiple levels hardware assurance, trusted boot, Multiple Independent Levels of Security (MILS) operating systems, Secure Hypervisor, and middleware foundations for the system and application software.
The optimum security response starts at the lowest level within the system, and provides the solid foundation on which to build.
Read more
Hardware Assurance constitutes the “root of trust” in developing security-conscious solutions. Incorporating tamper resistant technologies such as volume protection, anti-tamper sensory technologies, and encryption play a pivotal role in developing these security solutions. Memory sanitization capabilities also provide a means to erase memory contents eliminating potential vulnerabilities.
Trusted boot enables the security products by leveraging hardware and software techniques designed to ensure integrity for the embedded computing environment and assurance of this trusted environment during runtime operation as well as maintenance procedures.
Between the secure hardware and your secure application, you’ll be using a secure operating system. We work closely with those companies to ensure everything happens as it should.
Read More
Multiple Independent Levels of Security (MILS) operating systems, Secure Hypervisor, and middleware provide the foundation for system and application software. Abaco Systems has experience with each of these areas and maintains key relationships with vendors to enhance future products and help accelerate the adoption of these capabilities in a world of high-connected architectures.
Extending data security beyond the process platform, Abaco Systems has a long history of providing rugged networking solutions currently in use for airborne, naval and ground mobile applications. These products combine network connectivity with advanced security, firewall and intrusion detection/prevention. Certification of these products becomes a key component to a security program. Abaco Systems is aware of these certifications and has products available to meet certification to standards such as FIPS 140-1 level 2 and Common Criteria EAL4 MRPP.
In addition to supplying state-of-the-art secure platforms, Abaco Systems is working to develop the next generation of security technologies.